
The Runtime Firewall for AI Agents
Stop hallucinations from becoming breaches. Sevorix is the kernel-level enforcement engine that intercepts and blocks dangerous tool execution (SQLi, PII leaks, rm -rf) in <5 ms. We ensure no autonomous command runs without deterministic, bare-metal authorization.
Kill destructive agent actions in milliseconds.
Application-level guardrails rely on intent; Sevorix relies on physics. When an autonomous agent goes rogue, we sever the connection at the bare-metal level before the payload ever executes.
Agents have "God Mode" access but lack judgment. A single hallucination can wipe your production database in milliseconds.
Firewalls block bad IPs, but agents are trusted insiders. Traditional security is blind to lateral movement from authorized AI.
Human security teams react in days. AI attacks happen in milliseconds. You need a machine to fight a machine.
Stop hoping your LLMs behave. Enforce absolute boundaries at Ring-0 and generate the exact tamper-evident logs required by the EU AI Act and ISO 42001.
The Architecture of Control
Sevorix decouples "Intelligence" from "Action." Your AI models can hypothesize, hallucinate, or be manipulated—but they can only execute what your bare-metal policy allows.
Every AI tool call (SQL, Shell, API) and underlying system call is captured by the Sevorix runtime environment before it ever touches your critical infrastructure. We don't just monitor application intent; we monitor the OS kernel.
The Policy Engine instantly cross-examines the requested action against your exact security boundaries. We translate high-level GRC frameworks (like the EU AI Act, HIPAA, and NIST) into rigid, deterministic execution rules.
Authorized actions execute seamlessly. Unauthorized network requests, data exfiltration attempts, or destructive commands trigger the Deterministic Kill Switch. We sever the process at Ring-0 in <5 ms and generate a tamper-evident audit log. Zero human intervention required.
Execution Pipeline
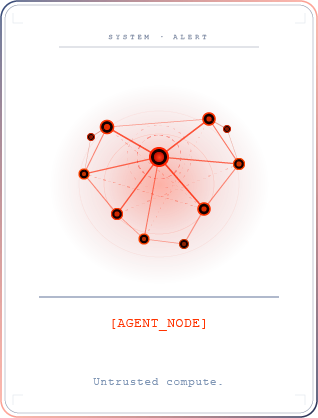
System-level interception of autonomous compute.
The operational layer houses dynamic AI frameworks like LangGraph, CrewAI, and AutoGen. Because autonomous agents are susceptible to prompt injections, hallucinations, and raw shell drops, Sevorix treats this entire node as fundamentally untrusted compute.
.png)
The unbypassable kill switch. Sitting at the OS layer, Sevorix intercepts every agent system call in <5 ms. It evaluates the action against deterministic enterprise governance policies, physically · severing unauthorized connections and file executions before they can occur.
(1).png)
.png)
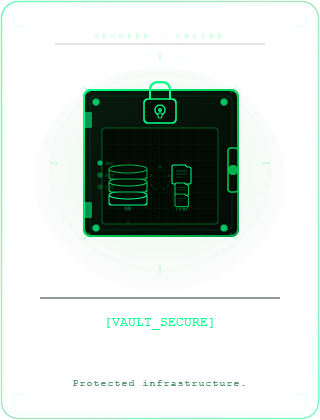
Your enterprise crown jewels. Internal databases, proprietary APIs, VPCs, and root files remain completely isolated from rogue AI behaviors. Sevorix ensures zero unauthorized outbound data exfiltration and blocks East-West lateral movement.
Operational Models
From localhost experimentation to air-gapped enforcement.
SEVORIX LITE

SEVORIX TEAM
SEVORIX ENTERPRISE
Frequently Asked Questions
What is a Runtime Firewall for AI?
Traditional firewalls protect networks. Sevorix protects actions. We sit at the OS kernel level, between your AI and your system tools. If an agent attempts a destructive command—whether due to a hallucination or a jailbreak—Sevorix severs the execution at the system call level before it can touch your data.
Will Sevorix slow down my agent?
Negligible impact. Built in Rust and operating via eBPF, our inspection latency is <5ms. We are designed for high-throughput agentic workflows where sub-millisecond enforcement is the difference between a secure system and a breach.
How does this differ from L7 Gateways (like MoCoP)?
L7 gateways manage "intent" and tool-call parameters. Sevorix provides the "execution" kill switch. If an agent is compromised and drops to a raw shell to bypass the gateway, Sevorix catches the unauthorized connect() or execve() system call at the kernel level. We are the muscle that enforces the brain's policy.
Does it work with LangChain, CrewAI, or AutoGen?
Yes. Sevorix is framework-agnostic because it operates at the host level, not the application level. Whether your agent is built on a popular framework or raw Python, Sevorix intercepts the execution pipeline directly. No code changes or middleware proxies are required.
Does Sevorix send my data to the cloud?
Sevorix Developer processes everything locally; no data ever leaves your hardware. For Enterprise, we offer a hybrid or fully air-gapped model. Enforcement happens in your VPC, and only anonymized metadata for compliance (SOC2/EU AI Act) is synced to the Watchtower dashboard.
Can it stop prompt injection?
Sevorix focuses on the “action,” not the prompt. Even if an attacker successfully jailbreaks your LLM, Sevorix analyzes the resulting system call. If the AI attempts to rm -rf a directory or exfiltrate a database, we block it based on policy, regardless of how the malicious prompt was engineered.
What is the “Jury of Rivals”?
This is our Pre-Execution Semantic Consensus engine for Sevorix Enterprise. While our eBPF firewall provides an inescapable physical floor, the Jury of Rivals evaluates the intent and admissibility of an agent's proposed action before the trigger is ever pulled. It uses multiple adversarial AI models to interrogate the proposal—if the consensus determines the action violates your enterprise logic, it is killed before it ever reaches the execution environment.
What kind of logs do I get for an audit?
Every block event generates a tamper-evident, cryptographically sealed log entry. These logs include the specific agent ID, the unauthorized system call, the timestamp, and the policy violated. This provides a clear chain of custody required for HIPAA, ISO 42001, and EU AI Act compliance.
Is it "Policy-as-Code"?
Yes. You can define allowlists (e.g., “Only allow SELECT on the ‘public’ schema”) or blocklists in simple YAML or JSON. These rules are hot-swappable and pushed from the Watchtower to your fleet instantly without requiring a restart of your AI agents.


